Introduction
Many people have used a sniffer at some time. What is a sniffer? A sniffer is an application that catches all network traffic from or to computers attached to a network. Basically, what a sniffer really does is pay attention to all traffic by putting a network interface in the promiscuous mode state. Promiscuous mode puts a selected network interface to listening to all packets passing through it.
This article demonstrates how an application can configure a socket connection to pay attention to all network packets, instead of only those addressed to it. It shows how to grab protocols encapsulated by IP (Internet Protocol: network layer protocol), specifically, TCP and ICMP. IP encapsulates up to 100 different protocols. I advise you to take a look at the RFC 1700, as there is a complete list of all protocols that IP encapsulates.
Let Us Start to Sniff
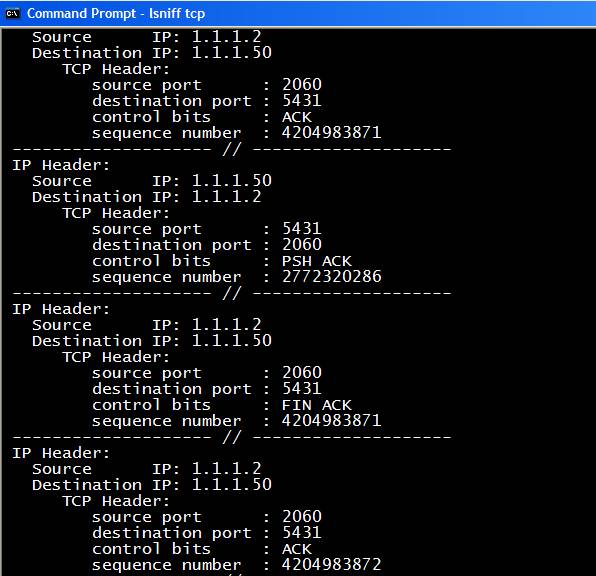
The demo project contains a single executable named lsniff.exe, which is a console application. The syntax is:
lsniff [TCP|ICMP]
TCP grabs TCP packets only (RFC 793).ICMP grabs ICMP packets only (RFC 792).lsniff, with no arguments, will grab TCP and ICMP packets.

Figure 1: example of lsniff grabbing only ICMP packets
You also can redirect the output to a file: lsniff icmp >output.txt
Understanding the Source Code
lsniff is a C/C++ application coded using Visual Studio 2005. It will compile in older compilers, too. It is really simple. In fact, the difficult part is to analyze the packets because you must know the packet structure that depends upon the protocol. Windows Socket API (WSA) offers the tools (functions) to create a simple sniffer.
It is worth mentioning that lsniff will run only if the you are logged on with administrative privileges. By reading lsniff_main.cpp, we will see the 4 necessary steps to start working in the promiscuous mode state:
Initialize Windows Sockets (line 107).
Get a RAW socket (line 111). RAW is a special type of socket that gives you access to packet headers, not only the data.
sniff_socket = socket( AF_INET, SOCK_RAW, IPPROTO_IP );
Bind the socket to the interface you want to sniff (line 119-127).
Set the socket to promiscuous mode (line 135).
if ( WSAIoctl( sniff_socket,
SIO_RCVALL,
&optval,
sizeof(optval),
NULL,
0,
&dwLen,
NULL,
NULL ) == SOCKET_ERROR )
{
printf( "Error: WSAIoctl = %ld\n", WSAGetLastError() );
exit(-3);
}
After all those 4 steps have been successfully performed, it is time to start reading the packets. Notice that you should provide a buffer big enough (LS_MAX_PACKET_SIZE) to the recv function. The first check made after a packet has been read is the IP version (line 161):
if ( LS_HI_PART(ip_header->ver_ihl) != 4 )
continue;
lsniff only parses IPv4 packets, not IPv6. Furthermore, the IP header is parsed to know what protocol is encapsulated. Notice that lsniff does not care about packet data, only packet headers. The rest of the code depends upon your knowledge about the protocol you want to parse. Of course, you can extend lsniff by adding more protocol-parsing routines. It is good practice to use a professional sniffer (like Ethereal) to help you to parse packets:

Figure 2: parsing packets
Enjoy. I hope this helps.
History
- 5 November, 2007: First version
